
While there are several global large security outcomes in the world, we’re now at the cusp of entrepreneurs building large companies in India and South East Asia. India and South East Asia are fairly early in this journey. Cybersecurity has never been more central and more complex. The market is large, growing and more resilient than other spaces during downturns. Organisations have ramped up their security spend significantly with younger startups adopting security solutions. The shift to cloud, remote work and developers responsible for security operations has only enlarged the opportunity at hand here for startups to seize. India has some unfair advantages given the technical and security talent present here which uniquely positions teams building from the region.
Rising inflation numbers have made the market volatile but there is a sector that is untouched by rising prices and slowing consumption: cybersecurity. A report by McKinsey has highlighted how damages due to cyberattacks will result in $10.5 trillion lost every year by 2025. In the first half of 2022, venture capital continued to flow into cybersecurity, according to the Momentum Cyber’s Market Review for 1H 2022. One reason is because cybersecurity increasingly became a top business concern, outweighing even price inflation, supply chain/logistics and the global IT talent shortage. After the various hacks of 2020, businesses realised they needed to invest heavily into buying more security products. Gartner forecasted that security spending will grow at 11.3% CAGR to a whopping $188.3B YoY. As a result of which, VC funding has ballooned in this space.
In H1 of 2022, ~$12.5B of capital was invested across 531 cybersecurity deals. To give you context, in H1 2021, that number was $12.6B and was by all counts a record year for investment. In fact, Q1 in 2022 ranks as the 3rd highest quarter of all time for financing volume, only behind the record-setting pace in 2021.
While there are several leading global startups in the space, India is just getting started. India has the highest number of ethical hackers in the world and this number has rapidly grown in the past few years, according to the 2020 HackerOne report. India also has the highest number of bug reports submitted (18%).
There are many reasons why we believe it might be the right time to be building in security globally:
- Newer security models with the move to cloud: The surface area for attacks has shifted with the move to containers and microservices enabling newer companies to be built here. Older products will not be able to directly use the security products that exist in the market today, given the fundamental shift in the architecture of applications and changing security posture.
- Bottom up motion possible: Early-stage teams have started thinking about security at initial stages, enabling a bottom-up GTM motion to be built within security. This, combined with the shift left movement in security, can unblock really fast-growing companies. With developers directly involved in maintaining the security posture of an organisation, security buying is changing.
- More sophisticated attacks: Adversaries of companies are no longer limited to individual actors. They include highly sophisticated organisations that leverage integrated tools and capabilities with artificial intelligence and machine learning. The scope of the threat is growing, and no organisation is immune. Small and midsize enterprises, municipalities, and state and federal governments face such risks along with large companies. Today’s most advanced cybersecurity products, no matter how effective, will soon be obsolete.
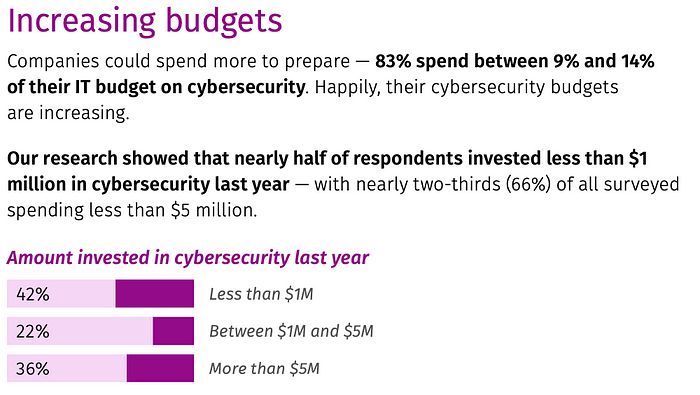
- Unsolved problem with increasing budgets: Around ~70% of organisations plan to increase their security budgets, and ~30% want to increase them significantly according to a report by Vanta. Hiring security experts, which has always been a tough task, is harder now, given the lack of availability of real experts.
Within security, there are several areas growing and emerging categories.
Cloud infrastructure security
The broader shift to cloud and cloud-native architectures means a completely new approach to security. This includes securing newer architectures, their supply chain and the configuration and goes far beyond the current cohort of vulnerability scanners in the market. Wiz, an Israel-origin cloud security startup ramped up to $100M ARR within 18 months and became the fastest-growing software company ever to do so.
The success and rapid adoption of Wiz has shown the gaps in terms of cloud security products in the market. Scrut automation and PingSafe are examples being built out of India focusing on proactive assessment of risks. Project Discovery is a startup building to quickly scan and monitor internet wide assets and vulnerabilities. Cloud infrastructure security is expected to grow at 27% CAGR YoY in 2023.
Application security
The number of third party SaaS apps that an enterprise uses has exploded in recent years, so have the number of open source dependencies in enterprise code. This leaves the opportunity for products to be built that can secure the usage of these third parties, both as SaaS applications as well as access within code. Code scanning tools, third party audit products and access management for third party software are typical whitespaces. Snyk (last valued at $8.5B) is a recent example in securing your code against vulnerabilities while developing and leveraging the shift left movement in security. There are approximately 750M new cloud native apps and all of those need to be secured.
Identity & access management
A big part of securing products is securing the way we access them, access our database and several other critical services. This is typically done via secrets and tokens in sessions between internal services, between users and services as well as APIs and third party services. With the move to cloud, security breaches related to secrets and tokens have increased at an alarming rate, with several common and uncommon issues such as a secret being disclosed publicly and used to access sensitive information. Secrets management, secret ops management and identity need to be rethought ground up. With the increasing number of SaaS applications, internal and external actors and increasingly complex cloud infrastructure and its access patterns, identity needs to be more natively integrated across these new workflows. Transmit Security is an emerging player in this category, simplifying policies across channels, devices, and applications via simple policies. It is rumoured to be at more than $100M run rate within 3 years of operation. The company announced the largest cybersecurity Series A funding round in history in June 2021, and has grown revenues by 40% year over year. Another emerging trendline in this category is the adoption of passwordless workflows. This is currently a ~$65B market supported by strong trendlines such as move to cloud, remote work and explosion in identities.
Data security
Discovery and audit of data silos, dark data, application data and configuration of these data stores is a challenge for organisations today. What makes this problem challenging is the increasing number of silos that data in an organisation can exist in. This also helps in simplifying some compliance use cases. This remains one of the biggest challenges and threats organisations face today. Lightspeed funded Normalyze security is building in this space.
Insider threat prevention
Human awareness issues and insider threats such as phishing, unintentional internal access and sharing of data or not complying with internal policies will also remain a focus for organisations. Businesses have started actively buying products to prevent email phishing, audit logging and security information and event management (SIEM) products. There are also gaps for new players via a wedge within data leak prevention, privacy and information protection. Moreover, remote work is here to stay and with a distributed workforce come new challenges of securing the perimeter. This opens up new opportunities within the access management and endpoint protection spaces while reducing the dependence on VPNs for secure access.
If you’re building in the security space, I would love to chat with you. Do reach out at manjot@lsip.com.
Authors




